By Jack Jackson, Sr NERC Reliability Specialist
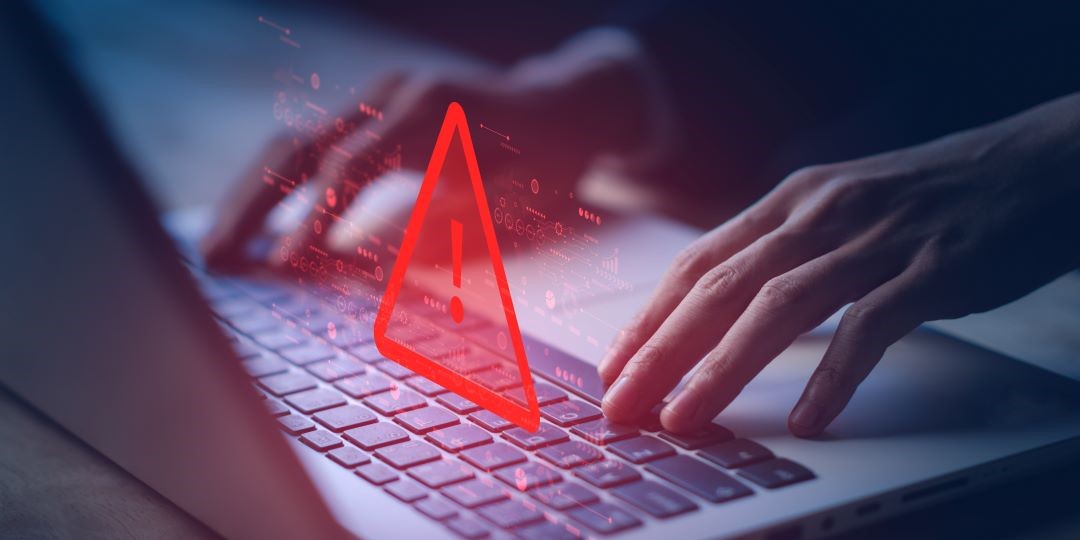
The landscape of Cyber Security is one of continuous change as more and more devices and components become “smart.” And the more “smart devices” there are deployed, the greater the opportunity is to lose control of one’s cyber security. While it is safe to say that most people strive to keep their data and devices secure whether personal or professional, comfort with smart devices can easily lead to complacency.
The Internet of Things (IoT) is a concept that was born as soon as the first appliance was connected to the internet back in the 1980s and the definition has continued to expand since then. Most recently it was recognized that with smart devices like home assistants (Alexa and Google Dot) getting themselves connected to a larger group of peripheral devices (thermostats, vacuums, baby monitors, refrigerators, security systems, etc.), we are either always listening or sharing data back to host systems. This poses a significant specific risk of manipulation via avenues such as social engineering with various phishing attacks.
In a similar fashion, Operational Technology (OT) is going in the same direction. The co-evolution of smarter data collection points and their ability to share data between multiple systems is creating a risk like that which we see in IoT. And, as the ability of OT to share information back to smarter mobile devices such as tablets and phones, the specific risk begins to develop where those portable devices become a bridge between OT and IoT.
Recent cyber security studies reveal that it is this developing overlap that poses one of the greatest risks to cyber security in the workplace. Those mobile devices that share personal and business data have the potential to cross populate user and system information and open vulnerabilities for various types of cyber-attacks. The significance is not that these vulnerabilities are new but the loss of awareness that the vulnerability is there increases the risk. And the more connected devices there are, the greater the risk to the industry.
Following is a list of recommendations from studies and industry experts to help minimize vulnerabilities in your connected world.
- In the workplace, designate specific mobile devices that are permitted to connect to OT and IoT and segregate these systems where possible
- Do not connect personal accounts to workplace mobile devices
- To the extent possible do not store contact information or business contacts on these devices
- Install VPN software to limit intrusion opportunities
- Install malware software for mobile devices to detect malicious code or intrusion
- To the extent possible do not share or link accounts with coworkers, friends, and families
To wrap up, the potential impact of smart and connected devices and systems is an ever-expanding vulnerability. In this forum we typically address concerns as they apply to the energy industry. However, this time, we should expand our vision to anywhere your smart device gets to talk to another device including the other smart devices in your own home. Bad actors don’t respect the boundaries between home, work, the hospital, or the grocery store. Don’t give them the edge.